What is two-factor authentication?
You may not have heard of two-factor authentication (also referred to as multi-factor authentication), but there is a strong chance that you are already using it. In its most common use, two-factor authentication (2FA) is used as an added security step for password protected systems. The password is the first authentication factor, and the second factor may be the answer to a secret question or a code sent to an email account.
Why is 2FA used?
The goal of 2FA is to increase security. Passwords can be broken, stolen or left exposed by a careless employee. The threat against passwords can come from inside your organization or from outside. With 2FA in place, a password gained improperly will not work on its own. The second authentication component is required for access. The goal is to ensure that you ARE you when connecting to your company's resources.
Challenges
If you have used systems that require secret questions, you have likely also been frustrated trying to keep track of the answers or spelling you used. Complexity, frustration and expense have been the largest challenges to adding 2FA to most small business systems.
Smart-Phones and Duo Security to the Rescue
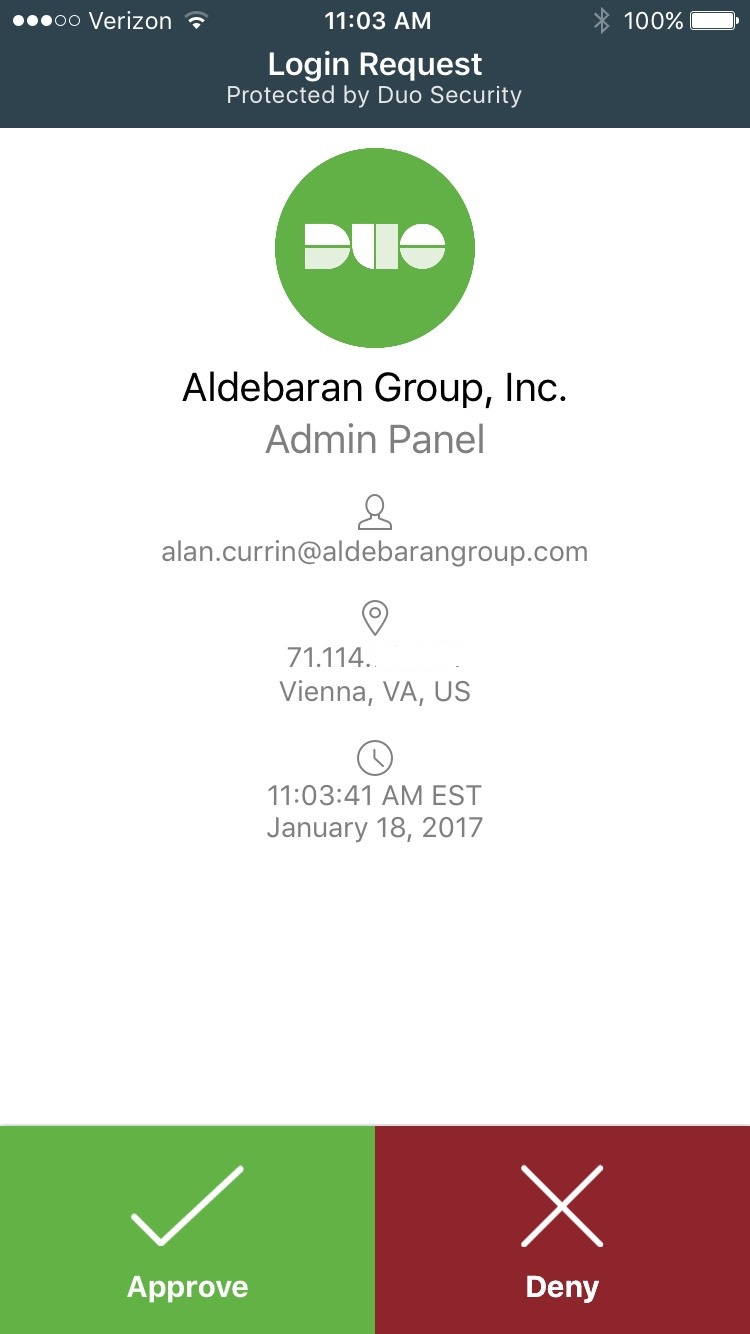
The proliferation of smart phones has put the power of communication in almost everyone's hands. A company called Duo Security has built an easy to use product that leverages a smartphone App, regular cell phones and even landline phones to test that you are who you say you are. To do this, a small software component is installed on your systems that triggers 2FA authentication when you try to access office resources such as a remote access server, Outlook Webmail or a virtual private network. After you successfully enter your network credentials, the Duo software installed on your network pauses the login process and requires that you validate the login using your smartphone's Duo App, a code can be sent to a regular cell phone, or a landline can be called. The notification appears on the smart-phone almost instantly and requires only a single tap to complete the login (in the example below, I simply tapped "Approve" and my login completed successfully).
My successful login required that all the following be true:
- I knew my login name
- I knew my password
- I had may smart-phone with me
- I knew my smart-phone password
Even if someone captures your password through malware, or tricks you into revealing it, they cannot access your accounts without approving access from your smart-phone.
Other Benefits
In addition to protecting your accounts, Duo:
- Notifies you via the approval prompt if someone is trying unsuccessfully to login under your username
- Logs the Internet address and location of each login attempt.
- Can limit logins by geographical location
Cost
Duo requires no investment in hardware and will merge easily into most technical environments. An Enterprise account costs only $3/user/month. The user fee does not increase if your firm chooses to protect more that one access point. For example, your firm can protect webmail, a remote access server and a VPN. The user fee is the only fee from Duo.
Get in touch today!
Email or call your regular consultant, or email: info@aldebarangroup.com, visit the Contact Us page on our website: https://www.aldebarangroup.com/contact-us/ , or call 202-683-6175 x 101 and leave a message for quick call-back


You must be logged in to post a comment.